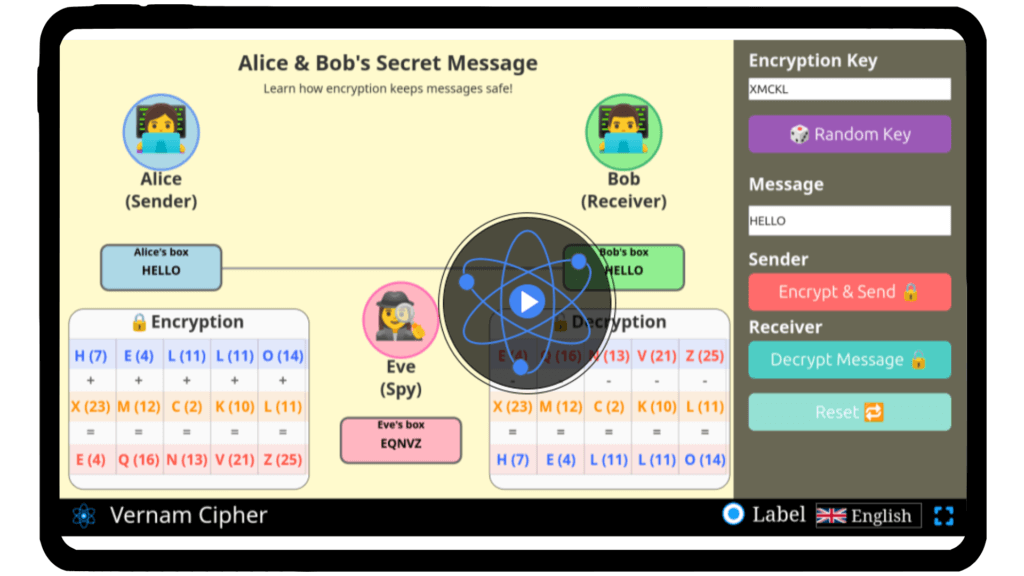
Verman Cipher Simulator
Investigate the logic behind the Vernam Cipher and experiment with different keys and XOR operations to observe how perfect secrecy is achieved using our interactive simulator.
Verman Cipher
Cryptography surrounds our digital world, securing countless messages we send every day, often in ways we never notice. Have you ever wondered how a perfectly secure message can be created using random keys? This fascinating method, known as the Vernam Cipher, relies on the principles of one-time pads and bitwise XOR operations. With our interactive simulator, you can explore this cipher firsthand. Enter plaintext, experiment with random keys, observe how ciphertext is generated, and understand the science behind unbreakable encryption. Start your journey into the intriguing world of cryptography — experiment with the Vernam Cipher today!
Mathematical description
The Vernam Cipher is a symmetric encryption method where each plaintext character is combined with a key character of the same length to produce ciphertext. This version outputs letters, not bits, making the cipher easier to read while maintaining a simple XOR-like operation on letters (mod 26 arithmetic).
Encryption formula:
\( C_i = (P_i + K_i) \bmod 26 \)
where:
Ci = ciphertext letter (A–Z)
Pi = plaintext letter (A–Z)
Ki = key letter (A–Z)
mod26 = ensures result stays within A–Z
Decryption formula:
\( P_i = (C_i – K_i + 26) \bmod 26 \)
Example (Text-Based):
Plaintext: HELLO
Key: XMCKL
Step 1 – Convert letters to numbers (A=0, B=1, … Z=25):
| Character | H | E | L | L | O |
|---|---|---|---|---|---|
| Number | 7 | 4 | 11 | 11 | 14 |
| Key | X | M | C | K | L |
| Number | 23| 12| 2 | 10| 11|
Step 2 – Encryption (mod 26 addition):
\( C_i = (P_i + K_i) \bmod 26 \)
| Plaintext | H | E | L | L | O |
| Key | X | M | C | K | L |
| Ciphertext| E | Q | N | V | Z |
Step 3 – Decryption (mod 26 subtraction):
\( P_i = (C_i – K_i + 26) \bmod 26 \) → Original text: HELLO
Note: For perfect security, the key must be random, equal in length to the plaintext, and used only once.
\(
\begin{array}{|c|c|c|c|c|}
\hline
\text{Position} & \text{Plaintext (P)} & \text{Key (K)} & \text{Ciphertext (C)} & \text{Decrypted Text (P)} \\
\hline
1 & H & X & E & H \\
2 & E & M & Q & E \\
3 & L & C & N & L \\
4 & L & K & V & L \\
5 & O & L & Z & O \\
\hline
\end{array}
\)
FAQs on Vernam Cipher
Qus 1. What is the Vernam Cipher?
The Vernam Cipher is a symmetric encryption technique that uses a random key of the same length as the plaintext to perform a bitwise XOR operation, producing a ciphertext that is theoretically unbreakable if the key is truly random and used only once.
Qus 2. What is the principle behind the Vernam Cipher?
The principle relies on the one-time pad concept: each bit or character of the plaintext is combined with a corresponding bit or character of the key using the XOR operation. Mathematically:
\( C_i = P_i \oplus K_i \)
where Ci is the ciphertext, Pi is the plaintext, Ki is the key, and ⊕ denotes XOR.
Qus 3. What are the main uses of the Vernam Cipher?
Securing highly sensitive communications, such as military or diplomatic messages.
Cryptography research and educational purposes.
Demonstrating the concept of perfect secrecy in encryption.
Qus 4. Who invented the Vernam Cipher and when?
Gilbert S. Vernam, an engineer at AT&T, invented the cipher in 1917. He originally designed it for teleprinter encryption using punched tape as a key.
Qus 5. Why is the Vernam Cipher considered unbreakable?
If the key is truly random, as long as the plaintext, and used only once (never reused), the ciphertext provides no statistical clues about the plaintext, making it theoretically impossible to break without the key.
Qus 6. What are the limitations of the Vernam Cipher?
Requires the key to be as long as the message.
Key distribution and management can be difficult.
Reusing keys compromises security completely.