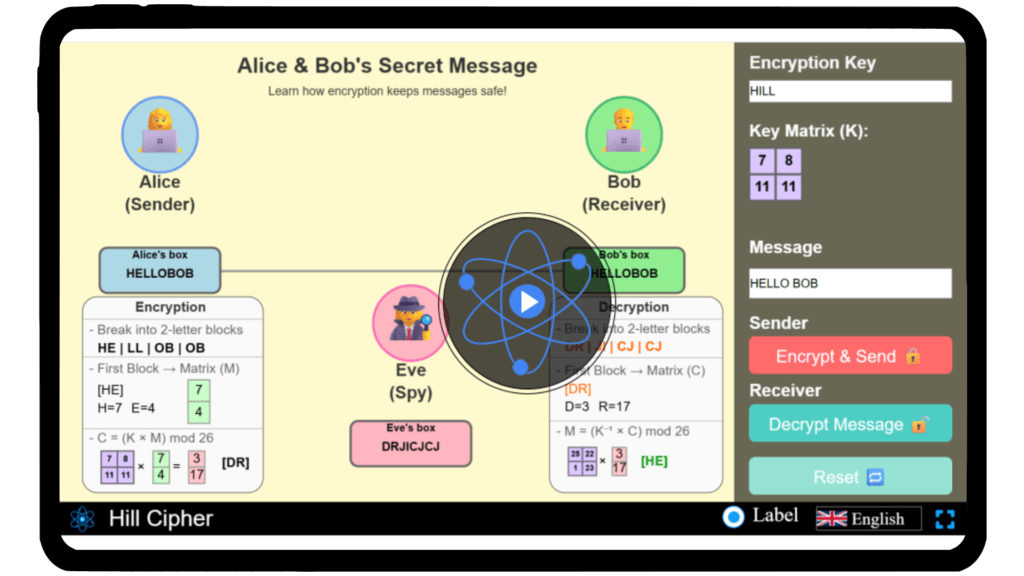
Hill Cipher Simulator
Investigate the mathematics of the Hill Cipher and experiment with different key matrices and plaintexts to observe how linear algebra powers encryption using our interactive simulator.
Hill Cipher
Mathematics surrounds us, securing the information we share every day—often in ways we don’t realize. Have you ever wondered how algebra and matrices can be used to encrypt messages? The Hill Cipher is a fascinating example of how linear algebra meets cryptography, transforming plaintext into coded form through matrix multiplication and modular arithmetic. With our interactive simulator, you can explore this cipher hands-on—build custom key matrices, encode and decode messages, and uncover the elegant logic behind its design. Step into the intriguing world of mathematical encryption — experiment with the Hill Cipher today!
Mathematical description
Encryption in the Hill Cipher is performed using the following formula:
\(C = K P \pmod{26}\)
Decryption is performed using the modular inverse of the key matrix:
\(P = K^{-1} C \pmod{26}\)
Where:
C is the ciphertext vector
P is the plaintext vector
K is the invertible key matrix (mod 26)
K⁻¹ is the modular inverse of K
Step 1: Convert letters to numbers (A=0, B=1, …, Z=25)
A = 0, C = 2, T = 19
Step 2: Represent plaintext as a vector
\[
P =
\begin{bmatrix}
0 \\
2 \\
19
\end{bmatrix}
\]
Step 3: Choose key matrix
\[
K =
\begin{bmatrix}
6 & 24 & 1 \\
13 & 16 & 10 \\
20 & 17 & 15
\end{bmatrix}
\]
Step 4: Encrypt using
\[
C = K P \mod 26
\]
\[
\text{Key matrix: }
\begin{bmatrix}
6 & 24 & 1 \\
13 & 16 & 10 \\
20 & 17 & 15
\end{bmatrix}
\]
\[
\text{Plaintext vector: }
\begin{bmatrix}
0 \\
2 \\
19
\end{bmatrix}
\]
\[
\text{Multiplication: }
\begin{bmatrix}
6*0 + 24*2 + 1*19 \\
13*0 + 16*2 + 10*19 \\
20*0 + 17*2 + 15*19
\end{bmatrix} \mod 26
\]
\[
\text{Result vector: }
\begin{bmatrix}
15 \\
8 \\
17
\end{bmatrix}
\]
Step 5: Convert numbers back to letters (A=0 → Z=25)
C = P, I, R
“ACT” is encrypted as “PIR”.
Step 1: Convert ciphertext letters to numbers (A=0, …, Z=25)
P = 15, I = 8, R = 17
Step 2: Represent ciphertext as vector
\[
C =
\begin{bmatrix}
15 \\
8 \\
17
\end{bmatrix}
\]
Step 3: Find modular inverse of key matrix
\[
K^{-1} \mod 26
\]
\[
K^{-1} =
\begin{bmatrix}
8 & 5 & 10 \\
21 & 8 & 21 \\
21 & 12 & 8
\end{bmatrix} \mod 26
\]
Step 4: Decrypt using
\[
P = K^{-1} C \mod 26
\]
\[
\text{Key matrix: }
\begin{bmatrix}
8 & 5 & 10 \\
21 & 8 & 21 \\
21 & 12 & 8
\end{bmatrix}
\]
\[
\text{Cipher vector: }
\begin{bmatrix}
15 \\
8 \\
17
\end{bmatrix}
\]
\[
\text{Multiplication: }
\begin{bmatrix}
8*15 + 5*8 + 10*17 \\
21*15 + 8*8 + 21*17 \\
21*15 + 12*8 + 8*17
\end{bmatrix} \mod 26
\]
\[
\text{Result vector: }
\begin{bmatrix}
0 \\
2 \\
19
\end{bmatrix}
\]
Step 5: Convert numbers back to letters (A=0 → Z=25)
P = A, C, T
The original plaintext “ACT” is successfully recovered.
FAQs on Hill Cipher
Qus 1.What is the Hill Cipher?
The Hill Cipher is a classical polygraphic substitution cipher based on linear algebra. It encrypts groups of letters using matrix multiplication and modular arithmetic, making it one of the earliest ciphers to use mathematics for cryptography.
Qus 2. Who invented the Hill Cipher?
The Hill Cipher was invented by Lester S. Hill in 1929. It was one of the first encryption techniques to use linear algebra and matrix theory to secure messages.
Qus 3.How does the Hill Cipher work mathematically?
The cipher converts plaintext letters into numerical vectors and multiplies them by an invertible key matrix (mod 26). The resulting product is then converted back to letters to form the ciphertext.
Decryption uses the inverse of the key matrix (mod 26) to recover the original message.
Qus 4. Why is the Hill Cipher important in the history of cryptography?
It marked the transition from simple substitution ciphers to mathematically grounded encryption. The Hill Cipher introduced the idea of using linear transformations, influencing the design of modern block ciphers and cryptographic algorithms.
Qus 5. What are the main applications of the Hill Cipher today?
While not secure by modern standards, the Hill Cipher is widely used for educational purposes to teach matrix operations, modular arithmetic, and the fundamentals of symmetric encryption.
Qus 6. What are the advantages of the Hill Cipher?
It encrypts multiple letters at once (polygraphic encryption), reducing frequency analysis attacks.
It uses linear algebra concepts, providing a clear mathematical model for encryption.
It’s easy to implement for learning and demonstration purposes.
Qus 7. What are the limitations of the Hill Cipher?
The key matrix must be invertible modulo 26, which restricts usable keys.
It’s vulnerable to known-plaintext attacks, making it unsuitable for secure communication today.
Qus 8. How is the Hill Cipher related to modern encryption?
The Hill Cipher inspired the mathematical framework behind modern symmetric key cryptography and block ciphers, where data is processed in groups using matrix-like transformations.